Identity Fusion Blog: IAM
Identity in the Age of AI: Why Governance Is the New Cybersecurity Imperative
In 2025, the stakes for Identity and Access Management (IAM) have never been higher. AI and machine learning are rewriting the rules of cybersecurity, and identity is at the..

The Emerging Future of Identity and Access Management: AI, Quantum Computing, and the Dawn of IAM 3.0
Part Two of Two As we saw in Part One, IAM is undergoing a seismic shift, from static, rules-based frameworks to dynamic, AI/ML-driven ecosystems that continuously evaluate risk..

The Emerging Future of Identity and Access Management: AI, Quantum Computing, and the Dawn of IAM 3.0
Part One of Two We all see that cyber threats are scaling faster than governance frameworks can adapt, the emergence of artificial intelligence (AI), machine learning (ML), and..
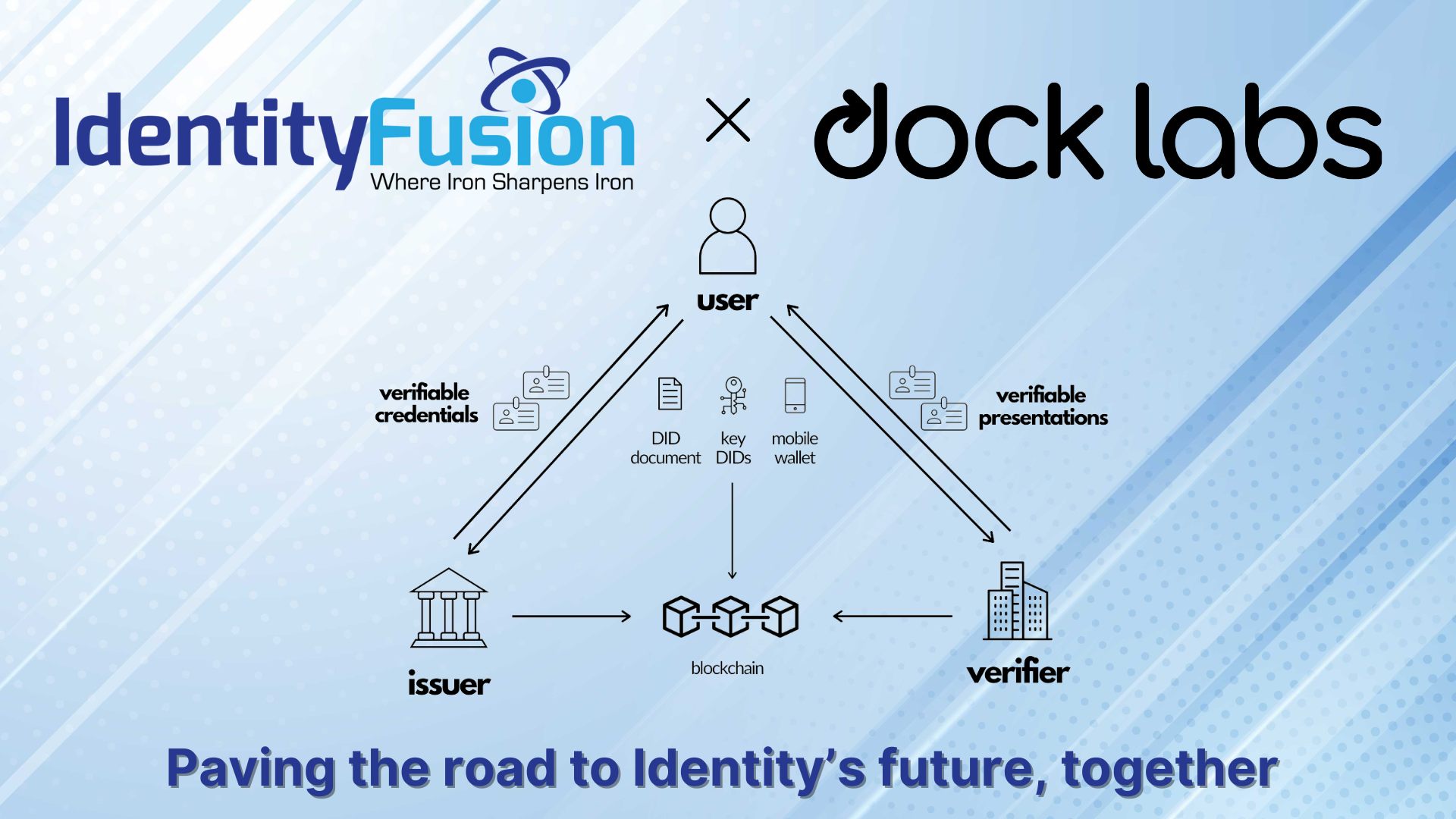
Identity Fusion Announces Strategic Partnership with Dock Labs to Bridge the Gap Between Legacy IAM and Next-Generation Identity Solutions
At Identity Fusion, our mission has always been to help organizations navigate the ever-evolving identity and access management (IAM) landscape with confidence and clarity. As..
The Rapidly Changing Landscape of AI in Identity
How 2025 Is Reshaping Automation and Security As we move deeper into 2025, the role of AI in identity is evolving faster than many predicted. At the start of the year, AI-driven..

TRUST, It’s not a new Concept
Trust in IAM should never be reduced to a marketing buzzword or a sales gimmick, it is the foundation upon which any identity and access management system must be built. The..

Future-Proofing Identity: Bridging the Gap to Identity 3.0
Identity security is more critical now than it has ever been. Organizations have invested heavily in legacy identity implementations, including enterprise directory services,..
New Year, New Beginnings: Embracing the Future of Identity and Access Management in 2025
As the calendar turns to 2025, organizations are facing a rapidly evolving digital landscape. With increasing cyber threats, expanding digital ecosystems, and rising consumer..
The Road to Identity 3.0: Challenges Associated with Implementing a New Identity Paradigm
Imagine a world where you never have to worry about your identity being stolen, where proving who you are is as easy as a tap on your phone, and where you—not some corporation or..

The Risks to Identity and Access Management (IAM) When Using Apps Like DeepSeek
Artificial intelligence applications like DeepSeek are growing in popularity due to their ability to provide advanced recommendations, language generation, and predictive..

The Increase of Device Based Cyber Attacks
The cybersecurity landscape has undergone a significant transformation in recent years. As multi-factor authentication (MFA) becomes the norm and encryption protocols strengthen,..

Why an IAM Assessment is Crucial for Your Cybersecurity Strategy
Today cybersecurity is not just about firewalls, antivirus software, or even penetration testing. While pen tests play an important role in identifying vulnerabilities from an..
