Identity Fusion Blog: Digital Identity
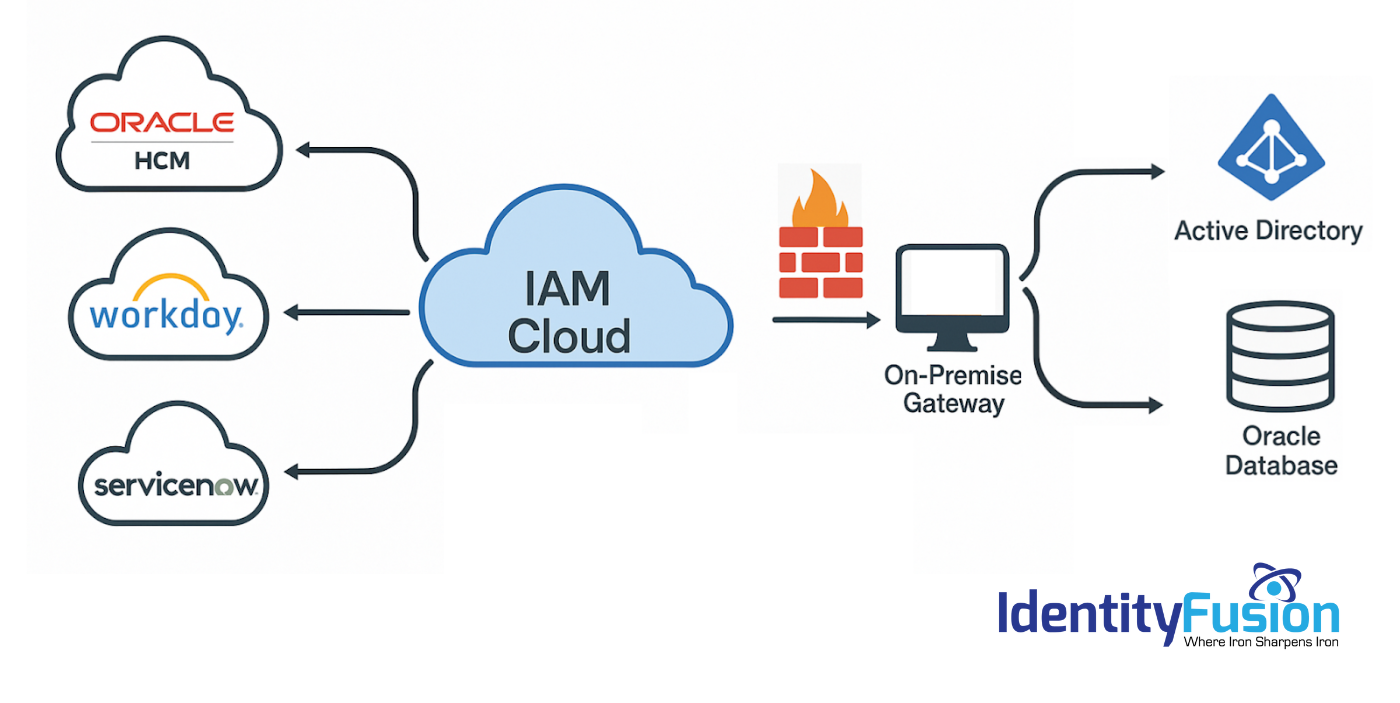
Migrating to an Identity Cloud: What the Vendors Won’t Tell You
As you explore the possibility of migrating your on-premise IAM solution to the cloud, you’ve likely heard promises of lower costs, simplified deployment, improved security, and..
Identity in the Age of AI: Why Governance Is the New Cybersecurity Imperative
In 2025, the stakes for Identity and Access Management (IAM) have never been higher. AI and machine learning are rewriting the rules of cybersecurity, and identity is at the..

TRUST, It’s not a new Concept
Trust in IAM should never be reduced to a marketing buzzword or a sales gimmick, it is the foundation upon which any identity and access management system must be built. The..
New Year, New Beginnings: Embracing the Future of Identity and Access Management in 2025
As the calendar turns to 2025, organizations are facing a rapidly evolving digital landscape. With increasing cyber threats, expanding digital ecosystems, and rising consumer..

Identity 2.0 vs Identity 3.0: A Comparative Analysis
As digital identity evolves, the limitations of traditional systems, often referred to as Identity 2.0, are becoming increasingly apparent. The rise of Identity 3.0 brings a..
The Road to Identity 3.0: Challenges Associated with Implementing a New Identity Paradigm
Imagine a world where you never have to worry about your identity being stolen, where proving who you are is as easy as a tap on your phone, and where you—not some corporation or..

The Increase of Device Based Cyber Attacks
The cybersecurity landscape has undergone a significant transformation in recent years. As multi-factor authentication (MFA) becomes the norm and encryption protocols strengthen,..

The Ghost of Identity Present: Exploring Modern Identity Solutions
In A Christmas Carol, the Ghost of Christmas Present acts as both a guide and a mirror, revealing the current realities of Ebenezer Scrooge’s life. By showing him the joys,..

The Ghost of Identity Past: A Reflection on Historical Identity Solutions
In Charles Dickens' A Christmas Carol, the Ghost of Christmas Past plays a pivotal role in helping Ebenezer Scrooge understand the foundations of his life. It transports him to..

Welcome to Identity 3.0: A Revolution in Digital Identity
The way we manage digital identity is under siege. Traditional identity and access management (IAM) solutions, often built around centralized databases and opaque processes, have..

Your New Digital ID: How Identity Wallets Are Redefining Trust in the Digital Age
Whether opening a bank account online, proving your identity at an airport, or verifying professional qualifications, we constantly need secure and reliable ways to assert "who we..
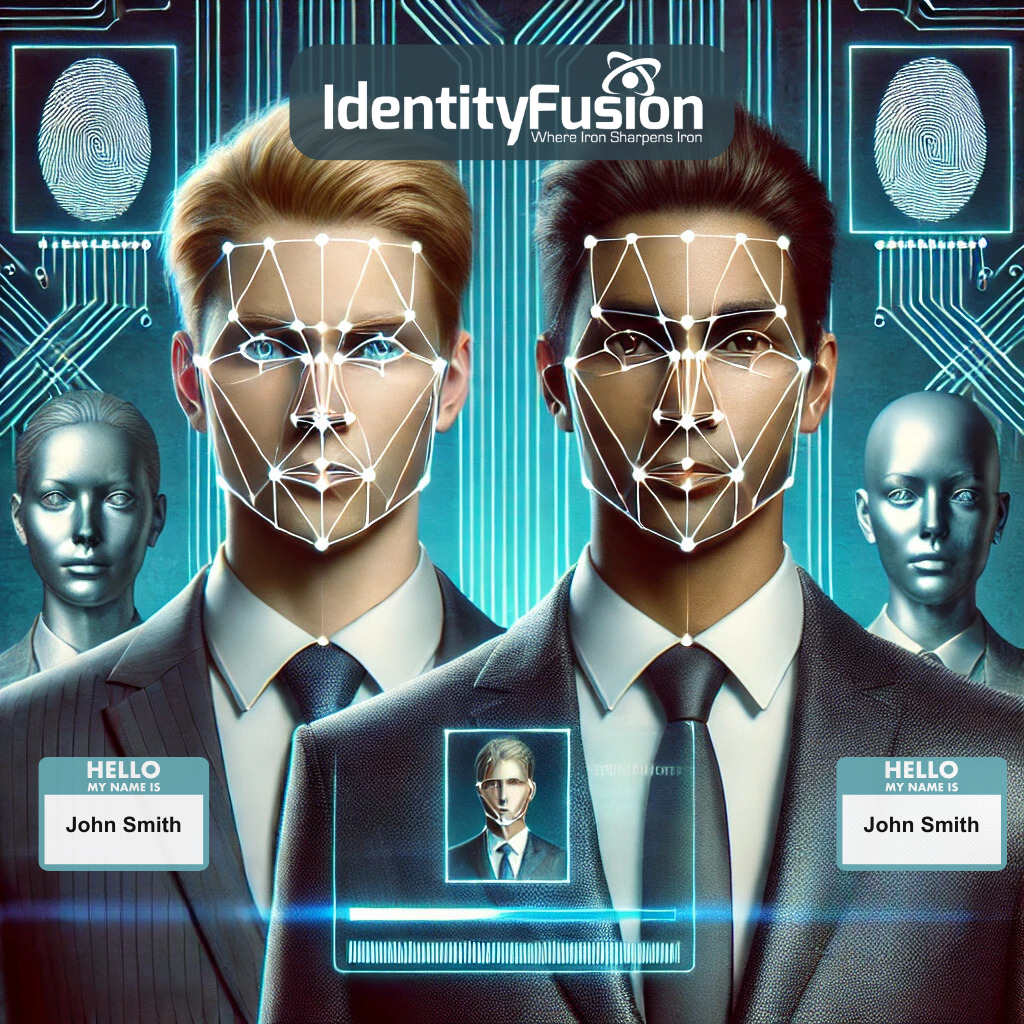
What’s in a Name - A Case for Verifiable Credentials
In today’s increasingly digital world, the importance of accurate identity verification has never been greater. Yet, many businesses still rely on outdated methods, using generic..
