Identity Fusion Blog
Identity Fusion Corporate Blogs & Articles
%20Management%20.png)
The State of Non-Human Identity (NHI) Management
As digital ecosystems grow increasingly complex, so too do the identities operating within them. No longer confined to human users, identity and access management (IAM) strategies..

The Strategic Value of Failing Early
Let’s be honest—technology is hard. Even the most seasoned teams, armed with detailed roadmaps, meticulous designs, and experienced architects, will eventually face the same..
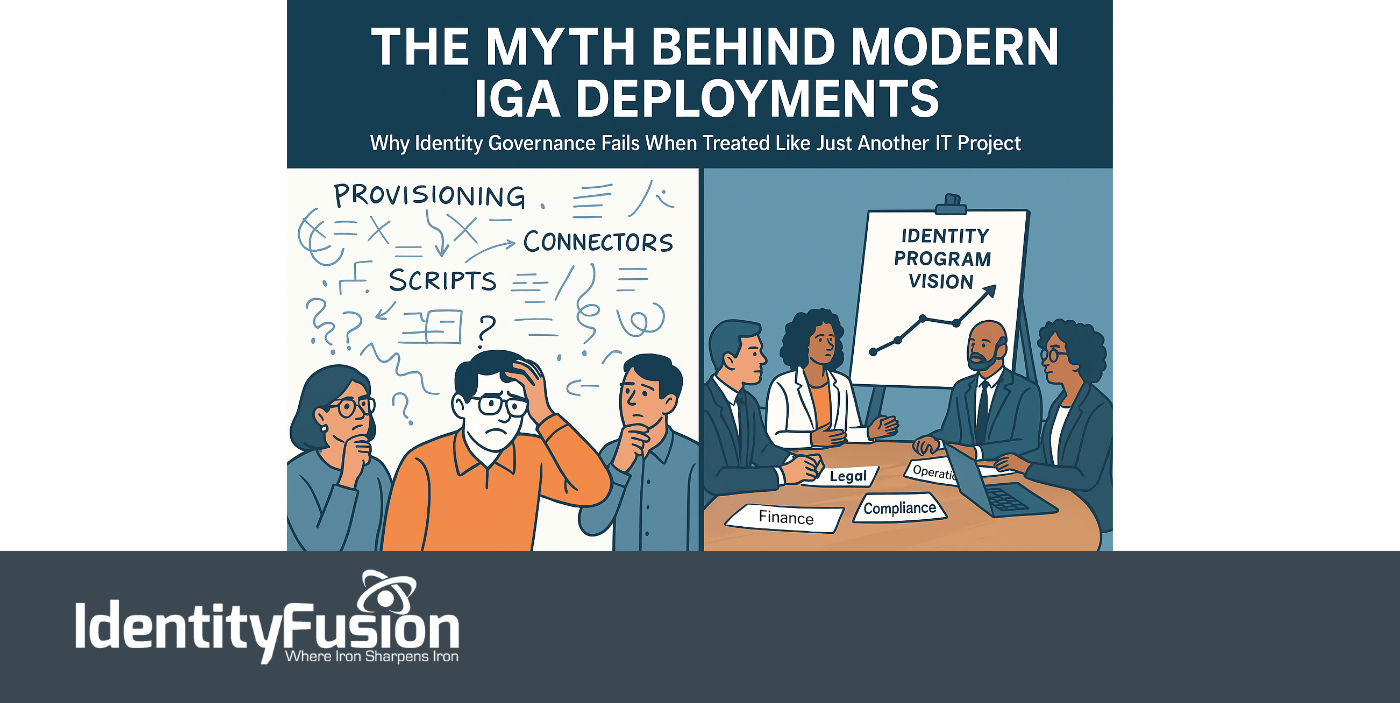
The Myth Behind Modern IGA Deployments
Identity is no longer just a security layer—it’s now central to everything an organization does. From onboarding employees and enabling partner collaboration to powering seamless..

Meet the Shakers and Movers of Identity at Identiverse — Las Vegas, Next Week
In an age when the world pivots on the axis of trust, those of us shaping the future of identity stand at a rare and vital crossroads. Next week, that crossroads has a name:..

Non-Human Identities: The Fastest-Growing Threat in IAM and Cybersecurity
In today’s digital battlefield, not all users are flesh and blood. In fact, most aren’t. The silent majority behind modern infrastructure, the service accounts, machine..
%20in%20Retail-%20Balancing%20Security%20and%20Seamless%20Experiences.png)
AI-Driven Identity and Access Management (IAM) in Retail: Balancing Security and Seamless Experiences
To today’s modern retailer, the customer journey is no longer limited to a single store visit or a static online cart. It spans apps, kiosks, mobile devices, loyalty portals, and..

Why Typical Agile Falls Short in Large-Scale Identity, Access, and Governance Projects
It is easy to appreciate why Agile has become the default project management style for so many technology initiatives. Fast iterations, continuous feedback, and adaptable..
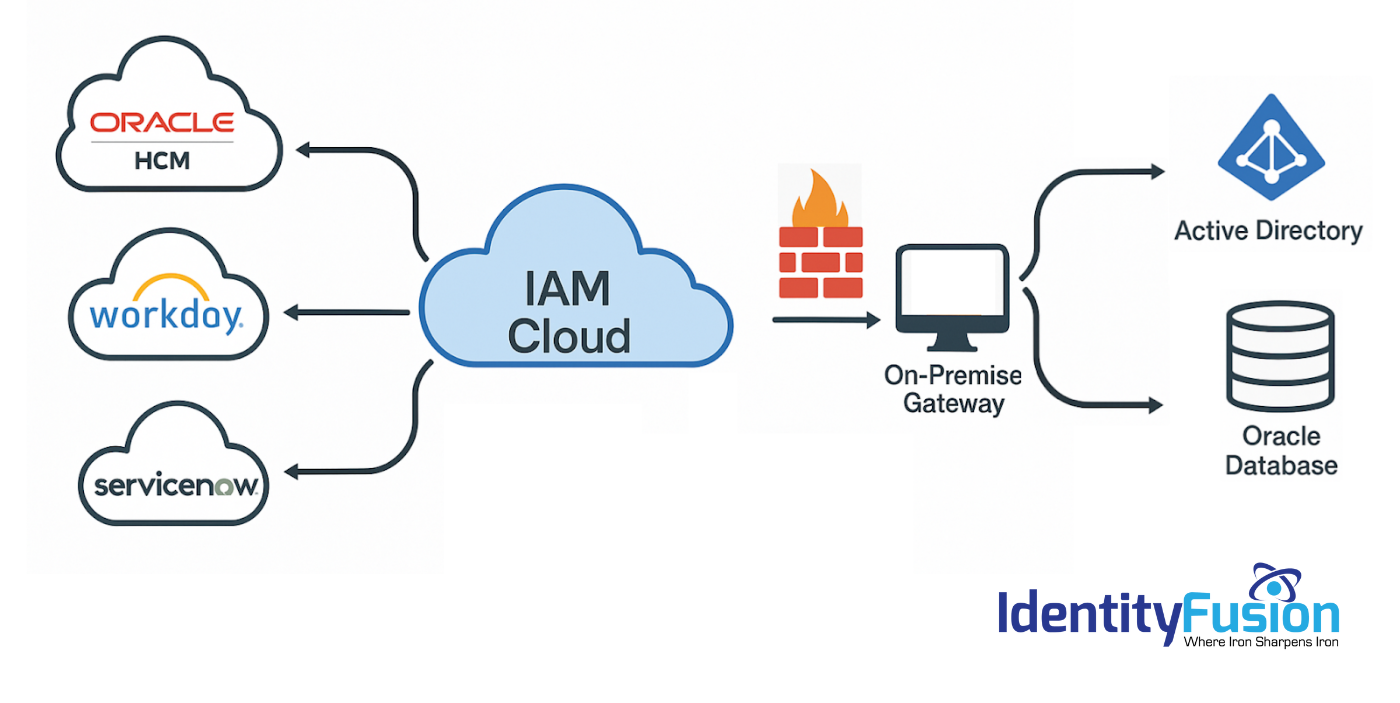
Migrating to an Identity Cloud: What the Vendors Won’t Tell You
As you explore the possibility of migrating your on-premise IAM solution to the cloud, you’ve likely heard promises of lower costs, simplified deployment, improved security, and..
Identity in the Age of AI: Why Governance Is the New Cybersecurity Imperative
In 2025, the stakes for Identity and Access Management (IAM) have never been higher. AI and machine learning are rewriting the rules of cybersecurity, and identity is at the..

The Emerging Future of Identity and Access Management: AI, Quantum Computing, and the Dawn of IAM 3.0
Part Two of Two As we saw in Part One, IAM is undergoing a seismic shift, from static, rules-based frameworks to dynamic, AI/ML-driven ecosystems that continuously evaluate risk..

The Emerging Future of Identity and Access Management: AI, Quantum Computing, and the Dawn of IAM 3.0
Part One of Two We all see that cyber threats are scaling faster than governance frameworks can adapt, the emergence of artificial intelligence (AI), machine learning (ML), and..

